Manufacturing only lags behind financial services and insurance in the frequency of data breaches. Companies are highly interconnected, ensuring that it remains more vulnerable to hacks than most other sectors.
According to one Sikich report, the rate of data breaches is continuing to rise. Fifty percent of companies say they’ve been victims of one or more data breaches in the last year. Eleven percent of these companies have endured a significant breach in the same period. Manufacturing become lucrative targets for cybercriminals because of their increasing reliance on IT. Any weakness in their networks is valuable for malware attacks, ransomware penetration, or cyberextortion.
Manufacturers with revenues under $500 million typically care less about critical cybersecurity preparedness. Less than half of these companies bother with regular cyber audits (38 percent), penetration testing (33 percent), vendor security assessment (32 percent), and employee phishing exercises (31 percent).
Case Studies of Cyber Attacks
A few important manufacturing data breaches can help you appreciate the potential negative impact of internet threats.
- Foxconn. If you’re reading this article from an iPhone, you’ll be grateful for China’s Foxconn. The manufacturing giant is responsible for producing components for Apple. Swagg Security once hacked Foxconn, releasing login credentials and other sensitive data for large tech companies. You can imagine the embarrassment for the companies affected.
- DuPont. DuPont once had its research exposed by an insider breach. The rogue employee had accepted an appointment from a competitor but made sure to download around 40,000 sensitive files to forward to their new employer. Investigations of abnormally high database utilization traced dozens of files to a laptop of the new employer's.
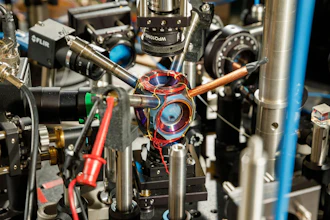
- Visser Precision. This space and defense manufacturer once succumbed to a DoppelPaymer ransomware attack. The ransomware encrypts and exfiltrates data. Sensitive company documents exposed key agreements pertaining to General Dynamics, SpaceX, and Tesla. There was even one Lockheed Martin schematic for a missile antenna. The company maintains the attack has zero impact on operations and no tangible cost implications.
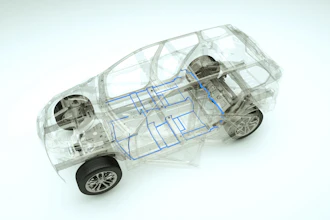
- Renault-Nissan. The infamous WannaCry ransomware was at the center of attacks on automobile manufacturer Renault-Nissan in 2017. It halted production at five plants in England, France, India, Romania, and Slovenia. The company managed to stem the tide of infection by disconnecting the infected plants from its network. The true scale of financial loss from this breach remains unknown.
- Apple. 2015 proved to be an unfortunate year for Apple, in that it experienced one of its most significant breaches of user account data ever. Keyraider, a malware, helped collect sensitive information from nearly a quarter of a million iPhone users across 20 countries. The malware exploits jailbroken iPhones, making abnormal app purchases.
- OXO International. The customer information of this New York manufacturer became public several times between June 2017 and October 2018. The scheme was possible due to malicious code on OXO’s website that could steal customer credentials and information from the company’s checkout page. It’s unclear how much customer data fell into criminal hands or the financial implications for the company. Customers got new login credentials and Kroll-provided identity monitoring services.
- FACC. In 2016, an attack was aimed at the accounting unit of FACC AG instead of the core manufacturing operation. The airplane component maker grossed more than $55 million in losses. In the FACC attack, an email purportedly from the CEO requested funds for an acquisition. Both the CEO and CFO lost their jobs as a fallout of the attack.
- Royal Dutch Shell. Shell had sensitive data related to 176,000 of its employees stolen. The compromised names and phone numbers belonged to the staff of the company in multiple countries worldwide. The breach was the work of "disaffected staff" who held reservations about the company's approach to business. Environmental and human rights groups received an email containing the data.
- Mondelez. A 2017 attack on Mondelez involved NotPetya, the encrypting malware. Mondelez is a food and beverage company with operations in many countries, and the attack destroyed 24,000 laptops, 1,700 servers, and production facilities worldwide. Mondelez was unable to fulfill customer orders as the attackers stole several thousand user credentials, consequently losing at least $100 million. The company's associates, FedEx, Maersk, and Rosneft, all lost hundreds of millions of dollars due to the NotPetya attack, and Mondelez sued its insurer, Zurich, for refusing to pay an insurance claim.
- Hanesbrands, Inc. The June 2015 attack on this U.S. clothing manufacturer is unique in the number of those affected – nearly one million. The company’s website was the source of the attack, the hacker disguising as a guest customer checking on an order. Addresses, phone numbers, and last four digits string of credit and debit cards of guest shoppers were stolen. Customer usernames, passwords, and corporate systems remained surprisingly secure for an attack that went on for up to one week.
How to Improve Your Cybersecurity
Manufacturers need to prepare for data breaches because it's not a matter of "if" as much as it's a question of "when" it will happen. Improving your cybersecurity to handle cyber attacks typically begins with implementing an incident response plan or IRP to ensure a fitting response in the event of a breach.
What will a suitable IRP cover? Preventative controls, rapid response to data security breaches, and prompt detection of possible problems are just a few components that should belong to your IRP. Companies have found that appointing a CIO (Chief Information Officer) and involving business continuity management in incident response lowered the cost of breaches per compromised record by 10 dollars and 13 dollars, respectively. A solid security posture will include:
- A Dedicated Incident Response Team. Choose individuals from departments that will play a role during a security breach. Executive Management, Human Resources, Information Technology, Legal, Operations, and Public Relations are probably the most crucial. Understand and specify the role of each team member and ensure they have authority to execute.
- Data Classification. Your incident response should consider each type of data the breach compromised. It's a necessary step to determine what happens as part of the incident response. Categorize data to help employees handle a variety of information effectively. "Confidential," "Internal Use Only," and "Public/Non-Classified" are appropriate data access levels. Take measures to secure your most confidential data.
- Plan Communications. Maintain a current contact list of IR team members, system support staff, and external service providers. Create appropriate messages for internal and external contacts after a breach.
- Training. Train Incident Response Team Members to evaluate, respond to, and manage security incidents.
- Testing. Advance continuous and thorough testing before an actual breach helps to spot issues in the process and assure that the plan will work in response to incidents.
Manufacturers are continually improving the automation of their operations. However, this opens them up to new kinds of problems, namely data breaches. A comprehensive security apparatus is no longer optional; it’s a necessity for the modern manufacturing enterprise.
David Lukić is an information privacy, security and compliance consultant at IDstrong.com.