Each day, another Internet of Things (IoT) security breach dominates the headlines. You name it, it has been hacked: smart cars, WiFi Barbie, refrigerators, thermostats and more. The recent DDoS attacks using a botnet of hacked consumer IoT devices is scary to say the least.
The lack of security in these devices is something that rests heavily on the minds of manufacturers, technology providers and resellers. Security, at the manufacturing level, is the key component to full realization of the IoT.
Manufacturers are always looking to improve the efficiency of the production line, whether that is through speed, eliminating bottlenecks and waste or accuracy of production. Manufacturing executives must be able to reduce waste, speed up automated processes and ensure quality remains high. Adding internet-connected machines and devices inserts additional responsibilities to this list: ensure data security, privacy and safety.
Strong Device Identity Is An Essential Component To Security
Every connected device in a manufacturing environment needs its own unique digital identity.
This digital credential establishes a root of trust, securely authenticates the device and ensures private communication with services. Working for a security vendor, I’ve spent a lot of time learning more about how manufacturers are provisioning device identities into their products and the challenges they have around this.
Today, there is still a lack of understanding and a lot of confusion in the industry around how best to manage identities and implement IoT security.
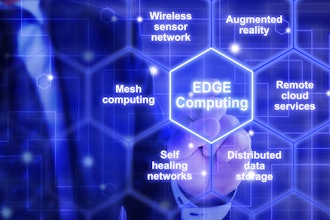
Managing Identities In The Cloud
Security in the Cloud is often met with a lot of skepticism and when talking about managing identities in the cloud, manufacturers often have a lot of questions: What if a cloud service suffers from a network outage and the production line is frozen? Is the Cloud really safe?
As a result, a lot of manufacturers are asking for an appliance-based solution that can be deployed in-house, but this can often be very expensive to develop, test and make tamper-proof. Additionally, there is a cost around maintenance, as this has to be done on site.

However, don’t be afraid of the Cloud. Find a Web-Trust Compliant, cloud-based certificate management platform that has redundancy, fail-over and disaster recovery built into the platform.
This means you can benefit from cloud-based value propositions including:
- Updates/fixes are done remotely.
- Services cannot be physically tampered with.
- Auditing and record keeping can be maintained safely offsite and requested at any time.
Best Time For Manufacturers To Provision Device Identity
The argument for using device identities to build trust and security into IoT ecosystems is clear, when to provision the device identity is less so.
Identity can be implemented during the manufacturing process, or when the device is turned on for the first time, at a seller store or in the owner’s hands.
For manufacturers, there are a few pros and cons to the different provisioning approaches, and it is important to decide which one is the best for the kind of product you produce and the type of customer you have.
1. Provisioning at the Time of Manufacturing
By provisioning identity to a device during the manufacturing process we are further decreasing the chance of an attack or vulnerability exploit.
The problem here is that time and cost will go into the production line. It's important here to think long-term as the initial stages might look more costly, but if you are leaving yourself less vulnerable to an attack, you are potentially appropriating huge cost savings as a result.
For example, FACC (an Austrian airline component maker for Boeing and Airbus) lost $54 million in a cyberattack. Or consider the massive damage a German steel mill suffered after a cyberattack on the mill’s control systems prevented the orderly shutdown of a blast furnace.
2. Provisioning at the Time of Device Wakeup
Generally, in this scenario, the customer uses their internet connection to access the cloud and install their device identity after the device is turned on for the first time. A benefit to provisioning at wake up is that it eliminates certain manufacturing environment complexities.

One potential problem with this approach is that you are shipping the device without identity and this in itself could be leaving devices vulnerable to attack. A smart connected thermostat being shipped without identity displaces some requirements on how you can appropriately enroll that device into required cloud services securely. How will your cloud services ensure that the device being enrolled is a trusted and authentic device, not a pirated clone or malicious node?
Despite some of the trade-offs, this method works particularly well when manufacturing devices such as gateway devices. A gateway device may want to wake up in the field in order to receive and bind information about its customer and ecosystem. As a result, it is sometimes easier to allow the identity to be provisioned at the time of wake up.
3. Identity During Manufacturing, Ownership at Wake Up
An alternative solution to the above is to provision the device identity during the manufacturing process, but then let the device provision ownership and authorization when it wakes up.
This ensures that inventory management is much easier. With this option it is vital to ensure that identities are being managed in one centralized platform to keep track of devices post-shipping.
Other Considerations For Manufacturers
Non-Transferrable Device Identity – Using secure hardware like a Trusted Platform Module (TPM) with a properly configured PKI environment to issue device identity certificates, manufacturers can have some assurances that the identity of a device can’t be transferred to another device.
Keeping Products Up-To-Date, Even Before Shipping - In today's fast paced "agile" software development environment, there is a benefit to loading the latest firmware onto devices before they go out into the field. Remote firmware upgrades are great and absolutely should be a part of the security design process.
However, they can be costly depending on the technical environment of the solution (e.g. the cost of upgrading millions of IoT devices over a cellular network for instance, or power usage of the firmware updates). Ultimately, you also need some core roots of trust established in the solution first, where identity is essential.
If manufacturers are able to pull-in the latest production firmware from the cloud, they can do better to ship devices with the latest firmware, another case to be made for smart internet-connected manufacturing.
Device Identity And The Cloud Will Save The Production Line
When adopting a cloud-based solution for identity management, you can save money by eliminating a need for an appliance-based solution, which will inevitably lead to more on site support and maintenance costs.
You can rely on an IoT security expert to maintain and update the cloud services, keep auditing and records safe, ensure devices are shipped with latest firmware and keep people from tampering with the service.
By provisioning identities, a manufacturer can ensure an even higher quality and more secure product reaches their customers, reducing piracy and fraud and improving both branding and customer trust.
Zachary Short is a principal software architect at GlobalSign.